Privacy-First, Compliance-Ready
Built from the ground up with security and compliance at its core. Emblema meets the highest regulatory standards while giving you full control over your data and AI operations.
AI Privacy Act Compliant
Our platform is fully compliant with the EU AI Act and global privacy regulations. Every AI decision is transparent, auditable, and under your control. We ensure that your organization meets regulatory requirements without sacrificing innovation.
- Transparent AI decision-making with full audit trails
- User consent management and granular data rights
- Automated compliance reporting and documentation
- Regular third-party security audits and penetration testing
- Data Processing Agreements (DPA) for all operations
- Right to explanation for all AI-generated outputs

Certifications & Standards
We maintain the highest industry certifications to ensure your data is protected at every level.
GDPR
Full compliance with the European General Data Protection Regulation for data privacy and user rights.
SOC 2 Type II
Independently audited controls for security, availability, processing integrity, and confidentiality.
ISO 27001
International standard for information security management systems (ISMS) certification.
EU AI Act
Compliant with the European Union's comprehensive regulatory framework for artificial intelligence.
Zero Trust
Zero-trust security architecture with continuous verification and least-privilege access controls.
E2E Encryption
End-to-end encryption for all data in transit and at rest, with customer-managed encryption keys.

Cloud-Native Architecture
Built from the ground up as a cloud-native solution, offering unparalleled scalability, reliability, and performance — while maintaining the security standards your enterprise demands.
- Microservices-based architecture for independent scaling
- Automatic horizontal scaling and intelligent load balancing
- Multi-region redundancy with 99.99% uptime SLA
- Container orchestration with Kubernetes
Auto-Scaling
Dynamically scale resources based on demand. Handle traffic spikes without manual intervention.
Multi-Region
Deploy across multiple regions for low latency and compliance with data residency requirements.
High Availability
Built-in redundancy and failover mechanisms ensure your AI services are always available.
Observability
Comprehensive monitoring, logging, and alerting for full visibility into system health.
Security Features
Enterprise-grade security at every layer of the stack.
Data Encryption
AES-256 encryption at rest and TLS 1.3 in transit. Customer-managed keys available.
Access Control
Role-based access control with SSO, MFA, and fine-grained permission management.
Network Security
VPC isolation, firewall rules, DDoS protection, and private endpoint connectivity.
Audit Logging
Comprehensive audit trails for all data access, modifications, and AI operations.
Vulnerability Management
Continuous security scanning, penetration testing, and responsible disclosure program.
Incident Response
24/7 security operations center with automated threat detection and response protocols.
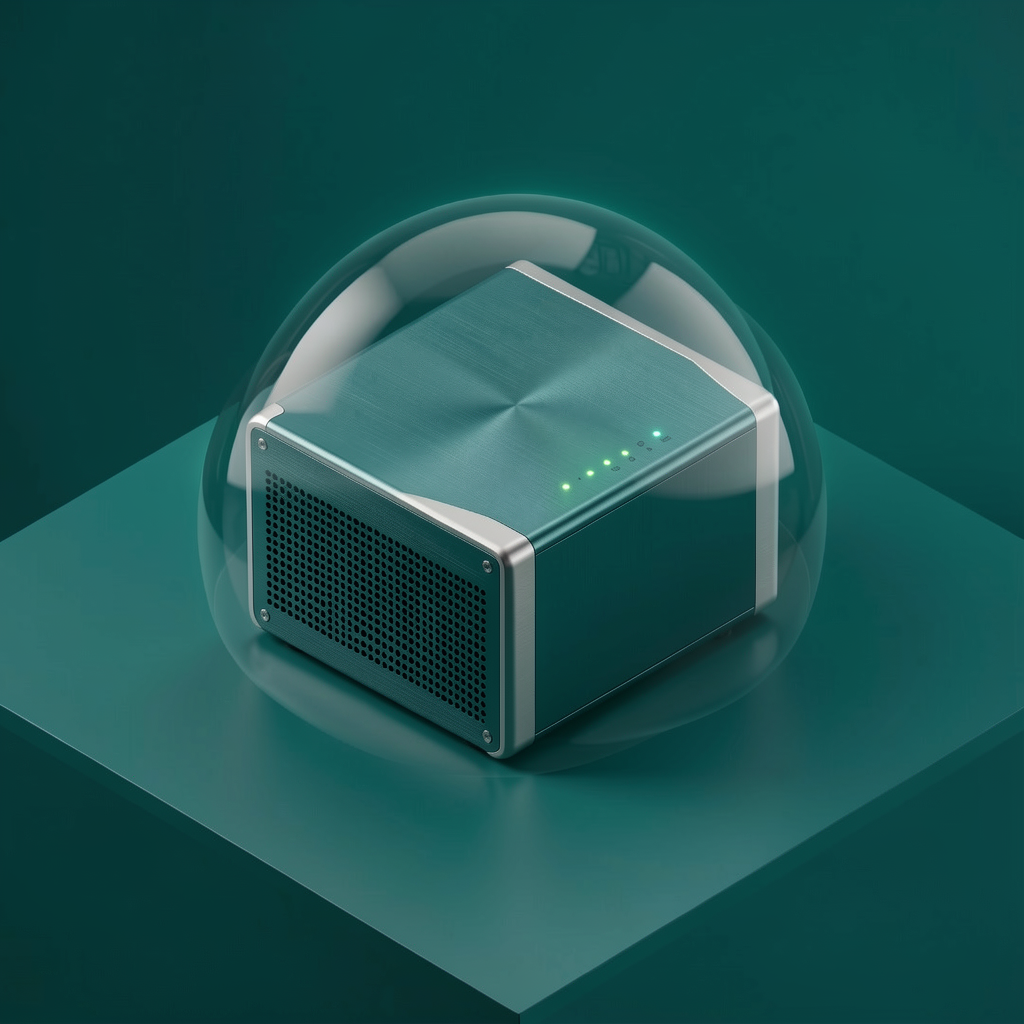
On-Premise Deployment
Deploy the entire Emblema ecosystem within your own private infrastructure. Complete data sovereignty, air-gapped options, and full control over your AI operations — without compromising on features.
- Air-gapped deployment for maximum security
- Full data sovereignty — your data never leaves your network
- Custom security configurations and integration
- Dedicated support team and maintenance SLA
Infrastructure Assessment
Our team evaluates your infrastructure and designs an optimized deployment architecture.
Secure Installation
Automated deployment scripts install and configure the entire stack in your environment.
Integration & Testing
Connect with your existing systems, SSO providers, and run comprehensive security validation.
Go Live & Support
Launch with confidence backed by 24/7 dedicated support and proactive monitoring.
Uptime SLA
Encryption
Data Breaches
Certified
Ready for Enterprise-Grade AI?
Contact us to discuss your security requirements and deployment options.
Contact Us